Best Non-Human Identity Management Solutions in 2026
Proper non-human identity management has become the backbone of enterprise security now that our digital environments are run more by machines than people.

Proper non-human identity management has become the backbone of enterprise security now that our digital environments are run more by machines than people. These identities, which include everything from service accounts and API keys to workload in containers and autonomous AI agents, are the invisible workers powering our cloud-native apps.
In many organizations…
…these machine identities now outnumber human employees by ratios as high as 45:1, and in some extreme cases, even 500:1.This big growth is a direct result of our push toward automation, where every new microservice or bot requires its own set of credentials to function.
The problem is that these "digital staff" often lack the strict oversight we give to human accounts, creating significant security holes that attackers are eager to exploit.
Since many of these identities bypass traditional multi-factor authentication and never "quit" their jobs, unmanaged machine access has quickly turned into one of the biggest risks for data breaches in 2026.
Managing these "invisible employees" is no longer optional for a secure stack, so I’ve put to the test the best best non-human identity security management solutions to help you get your machine access under control.
What Is Non-Human Identity Management (NHIM)?
Think of NHIM as the system for overseeing every digital key and credential that isn't tied to a person. It handles the entire lifecycle of these automated workers, from the moment they're created to the second they're deleted, to make sure every bot has a clear owner and doesn't have more power than it actually needs.
Human identity management (IAM)
Standard IAM is built for people, so it relies on things like passwords and biometrics to verify who is logging in.
It follows a predictable human timeline: an account starts on a person's first day at work and gets shut down when they quit or move on. Because people usually stick to a routine, it’s fairly easy for a security team to notice if someone suddenly tries to log in from a different country at 3:00 AM.
Non-human identity management
This is a different beast because it deals with machine identities that work around the clock at speeds humans can’t touch.
These identities use technical secrets like API tokens that don't play nice with traditional MFA, which makes non human identity security a much more technical challenge. Since there isn’t an HR department to tell you when a bot is finished with its project, a huge part of NHIM is finding these "zombie" accounts before they get used for a breach.
Key components:
When you're trying to lock down your non human identity landscape, you really need to focus on these three things:
- Identity creation and lifecycle management: You need a way to track a bot from its first line of code until it’s officially retired so it doesn't just hang around in your system forever.
- Authentication (keys, tokens, certificates): This replaces the usual password with machine-level credentials like rotating API keys to prove a service is actually what it claims to be.
- Authorization and access control: This defines the "fences" for what an identity can do, making sure a simple data-entry bot can't accidentally wander into your most sensitive financial records.
5 Types of Non-Human Identities
We’ve moved far beyond the days when a simple list of usernames and passwords covered your bases. Today, non human identities come in a few different flavors, and each one requires a specific approach to non-human identity security to keep things from getting messy.
Service Accounts
These are the workhorse credentials used by your internal apps to run background jobs or talk to databases without a human having to log in. They are notorious for being "set and forget" accounts, meaning they often sit there with high-level access for years without anyone ever checking if they’re still needed.
API Keys & Tokens
This is how your software talks to other software, serving as a digital passport for machine-to-machine communication. The big issue here is "secret sprawl", developers often generate these keys in a hurry and accidentally leave them in public code folders where hackers can easily grab them.
Workloads & Containers
In any modern cloud setup, every single microservice or container in your cluster needs its own identity to function. These are incredibly fast-moving, often appearing and disappearing in seconds, which makes it a nightmare to keep an accurate inventory of what they’re allowed to touch.
Bots & Automation Tools
Whether it’s an RPA bot doing data entry or a pipeline deploying your latest code, these tools need some of the most powerful access rights in your system. If you don't rotate these credentials constantly, a single compromised bot can give an attacker a clear path to move through your entire tech stack.
IoT Devices
This covers all the physical hardware connected to your network, like office cameras, smart sensors, and edge devices. Most of these ship with pretty weak security out of the box and don't get updated often, making them one of the easiest targets for anyone looking to mess with your non human identities.
Why Non-Human Identity Security Matters

Locking down these automated credentials is a top priority because a single unmanaged bot can basically hand over the keys to your entire network before you even finish your morning coffee.
NHIs often have over-privileged access
When a developer sets up a new bot, they almost always give it full admin rights just to make sure it works without hitting annoying permission errors during the build. This creates a massive headache called "permission creep," where a simple service account ends up with enough power to wipe out a database or change your deepest security settings.
Since there's no person sitting there to catch a weird file request, an over-privileged non human identity can do a ton of damage long before any alarms go off.
Lack of visibility and ownership
This happens every single day: someone creates a machine account for a quick weekend project and then completely forgets it exists once the job is done.
These "zombie" accounts are a goldmine for hackers because they don't have an owner and usually stay active for years. Without a heavy focus on non-human identity security, these abandoned accounts sit in the background like wide-open back doors just waiting to be exploited.
Long-lived credentials increase risk
Unlike employees who use face ID or change their passwords every few months, machine identities often rely on static API keys that literally never expire.
Every day that a key stays exactly the same is another chance for it to show up in a data leak or get pulled from an old script on GitHub. Once an attacker gets their hands on that kind of persistent access, they can walk right into your network without ever having to solve a single MFA prompt or security challenge.
Real-world impact:
Ignoring your non human identities usually leads to a few specific disasters that are a nightmare to clean up:
- Data breaches: A leaked token often gives a hacker a direct path into your customer files, letting them steal data for weeks while everyone thinks the system is running perfectly.
- Supply chain attacks: If an attacker gets into a third-party account that your system already trusts, they can easily hop into your internal network and move around without being seen.
- Cloud misconfigurations: A script with too much power can accidentally turn off your firewall or make your private storage public, putting your most sensitive docs out on the open internet with a single bad line of code.
Key Security Risks in Non-Human Identities
Leaving your machine accounts to their own devices is a fast way to open up massive security gaps that are hard to close later.
Credential Sprawl
This mess happens when developers hardcode secrets right into their codebases just to get a service moving. Once those keys are committed to a repository, they leave a permanent digital trail. Even if you try to delete them later, they often stay buried in the version history where any hacker with a basic scanner can find them.
Lack of Rotation
Static API keys and tokens that stay the same for years are a major failure in non-human identity security. Because these keys never expire, a single leak becomes a permanent problem. It gives an attacker a "forever" pass into your systems, letting them hang around your network for months without ever being noticed.
Excessive Permissions
Most machine accounts have way more power than they actually need to function. It’s a total violation of the least privilege rule, but it happens because people find it easier to grant full access than to figure out the exact permissions.
If one minor bot gets compromised, the attacker suddenly has the keys to your most sensitive data.
Poor Visibility & Monitoring
It is shockingly easy to lose track of which non human identities are actually running in your environment. These "orphaned" accounts are essentially unlocked back doors that don't show up on your standard security dashboards. Since nobody is watching them, they can be exploited for a long time before anyone even thinks to check the logs.
Secrets Exposure
Credentials leak out constantly through build logs, public repos, or even poorly secured CI/CD pipelines. It only takes one small mistake in a config file to put your most important secrets out on the open web.
Once that happens, automated scripts will scrape those keys in seconds, long before your team can hit the kill switch.
Core Principles of Non-Human Identity Management
Setting up some basic ground rules for your bot accounts now will save you a massive headache later on.
- Least privilege access: Never give a bot more power than it needs to finish its specific task. Keeping permissions tight means if an account gets hijacked, the hacker is stuck in a tiny corner of your network.
- Just-in-time (JIT) credentials: This creates a key only when a bot actually needs it and kills it the second the job is done. It’s easily the best way to stop leaving digital doors hanging open 24/7.
- Secret rotation and expiration: API keys and tokens should never live forever. They need a forced expiration date. Automated rotation makes stolen keys useless almost immediately and cleans up your security landscape.
- Identity lifecycle management: You need to track every machine identity from its first line of code until the day it’s officially retired. This stops "zombie" accounts from sitting in your system with active permissions for years.
- Continuous monitoring and auditing: Logging every action a bot takes helps you spot weird behavior, like a script suddenly touching files it shouldn't. This gives you a clear paper trail that is vital for both security audits and catching breaches early.
Non-Human Identity Management Solutions
Sorting through all the tech available to manage machine identities is a bit of a project, but most of it fits into a few specific buckets.
Secrets Management Platforms
Think of these as high-security vaults that keep your API keys and certificates safe so they aren't just sitting in plain text or buried in a random script.
Identity Governance & Administration (IGA)
This part of your stack handles the actual rules, making sure every single account is tracked and follows company policy from its first day to its last.
Privileged Access Management (PAM) for Machines
PAM tools are there to guard your most dangerous identities, the ones with enough power to reach into your sensitive data or change your core configurations.
Workload Identity Platforms
These are built specifically for cloud-native setups, giving every microservice or container a unique, verifiable identity so they can talk to each other without you having to step in.
Observability & Threat Detection Tools
This is your alarm system. It watches for weird behavior, like a bot suddenly trying to download a massive database in the middle of the night.
Solutions like Synk.to help unify visibility, automate identity governance, and secure machine-to-machine interactions across all your environments. Getting everything into one view like that is really the only way to keep your automation from becoming a major security liability.
Best Practices for Securing Non-Human Identities
Cleaning up the pile of machine identities on your network isn't that hard if you just stick to these habits.
- Stop putting secrets in your code. It is a huge mistake to leave API keys or passwords sitting in plain text in your source code or config files. Move those credentials into a dedicated vault so they aren't leaked every time a dev pushes a commit to GitHub.
- Keep permissions tight. Only give your bots the bare minimum access they need. If a service account is just there to upload one specific file, don't give it full admin rights over your cloud. Keep it in a tiny lane so it can't cause a disaster if the account gets hijacked.
- Rotate your keys. You have to put your tokens and certificates on a strict, automated rotation schedule. Shortening how long these keys stay active makes stolen data useless long before a hacker can actually do anything with it.
- One dashboard, not ten. Stop trying to track bot accounts across ten different spreadsheets or platforms. If you pull everything into one central spot, it’s much easier to see who has access to what and finally kill off "zombie" accounts that should’ve been deleted months ago.
- Log everything. You have to record every request and action your non-human identities take. Keeping these logs in a searchable place helps you spot weird behavior immediately and gives you a trail to follow if you ever have to investigate a security incident.
- Verify every single request. Just because a request comes from inside your own network doesn't mean it’s safe. Every machine-to-machine interaction needs to be authenticated every single time, which is the only way to stay secure in 2026.
Challenges in Non-Human Identity Management
Trying to keep a lid on machine accounts gets complicated fast because they don't follow the same rules as people and they grow at an insane rate.
- Scale and complexity: You likely have ten times more bots than actual people working at your company. Trying to keep tabs on thousands of identities is a total nightmare when they’re constantly spinning up or shutting down in the background of your automated tasks.
- Multi-cloud and hybrid environments: Running a mix of local servers and different cloud providers means you're dealing with three or four different ways of handling security. Getting your AWS roles to sync up with Azure or your on-prem data center is a constant, manual headache that never really ends.
- Lack of ownership and accountability: A lot of the time, nobody actually knows who is responsible for a specific bot. Developers often create a quick service account to get a job done and then just forget it exists, leaving "orphaned" identities with active permissions that no one is even watching.
- Integration with legacy systems: Modern security tools work fine for new apps, but they usually fall apart when you try to plug them into old, crusty software. Since these older systems weren't built for current protocols, you're usually stuck manually managing passwords for a database that should have been retired a decade ago.
Akeyless: SaaS-Based Secrets Platform
Akeyless is a cloud-native option that handles your secrets without making you manage a single backend server. It uses a zero-knowledge encryption setup to keep your data private from the provider, which is perfect for teams that need to keep machine credentials safe across a hybrid environment.
Key Features
- Secrets Management
- Secure Remote Access (SRA)
- Certificate Lifecycle Management (CLM)
- Encryption and Key Management (KMS)
- Software Supply Chain Security
Pros
- There are zero servers to patch or maintain because it’s a fully managed SaaS.
- The consumption-based pricing means you only pay for what you actually use.
Cons
- The web interface can feel a bit clunky or overwhelming when you first log in.
- It lacks some of the deeper session recording features found in high-end legacy PAM tools.
Ideal for: DevOps teams and mid-sized companies that need to automate secrets fast without the headache of managing their own infrastructure.
Doppler: Developer-First Secrets Management

Doppler is a solid pick if you’re sick of passing .env files around or accidentally leaking keys into your Git history. It basically functions as a central hub that keeps your dev machine and production servers in sync, so you aren't stuck manual copy-pasting every time a config changes.
Key Features
- Automated Secrets Sync
- Native CLI for Runtime Injection
- Versioning and Point-in-Time Rollbacks
- Change Requests and Approval Workflows
- Secret Health Monitoring and Masking
Pros
- The CLI is great because it handles the boring stuff like pulling keys into your environment variables without you touching a config file.
- Since it updates in real-time across your stack, you can push changes without the usual headache of manual service restarts.
Cons
- You can't host this yourself, which is a dealbreaker if your company policy forbids putting keys on a third-party SaaS.
- The seat-based pricing can hit your budget pretty hard once your engineering team starts to scale up past a dozen people.
Ideal for: Startup engineering teams that need to ditch messy local configs and want a tool that stays out of their way.
Infisical: Open-Source Secrets & Identity

Infisical is a fast-moving project that has become a go-to for teams wanting a transparent alternative to the big enterprise vaults. It’s built on an open-source model, which is a major win for developers who want to actually audit the code they are trusting with their machine credentials.
Key Features
- End-to-End Encrypted Secret Storage
- Dynamic Secrets and Automated Rotation
- Native Kubernetes Operator and Infisical Agent
- Certificate Lifecycle Management (PKI)
- Privileged Access Management (PAM)
Pros
- You can self-host the entire thing on your own hardware, which is great for staying in total control of your data.
- The MIT license protects you from the sudden licensing changes we've seen with other big names in the space.
Cons
- If you go the self-hosted route, the maintenance and patching are entirely on your plate.
- It's a younger project, so you might find fewer community-built plugins available compared to legacy tools.
Ideal for: Engineering-led teams and startups that prioritize open-source transparency and need a flexible, self-hostable way to manage secrets.
Cerbos: Policy-Based Access Control
Cerbos is a lightweight authorization layer that pulls your access logic out of your code so it can live in its own space. Instead of writing endless if-else chains to check permissions, you define everything in YAML policies that the engine evaluates in milliseconds.
Key Features
- Stateless Policy Decision Point (PDP)
- Cerbos Hub for CI/CD policy distribution
- Cerbos Synapse for data enrichment
- Full decision context audit logging
- Policy governance for AI agents
Pros
- You can push security policy updates on the fly. No need to restart your apps or push new code just to change a permission.
- The stateless design means it scales horizontally with zero effort, whether you're in Kubernetes or at the edge.
Cons
- It doesn't handle authentication. You’ll still need a separate tool to manage user identity and tokens.
- YAML is easy to read, but managing a massive library of complex policies gets messy fast if your naming conventions aren't spot on from the start.
Ideal for: Product and security teams that need to manage complex, fine-grained permissions across different services and AI agents.
Permit.io: Fine-Grained Authorization (RBAC/ABAC)

I’ve spent some time digging into Permit.io, and it’s a pretty smooth experience if you’re tired of manually coding permission logic. It essentially acts as a full-stack authorization layer that sits on top of open-source engines like OPA or Cedar.
The standout part for me is how it takes those complex policy-as-code concepts and wraps them in a no-code UI, so you aren't the only person in the company who knows how to change a user's access level.
Key Features
- No-Code Policy Editor (RBAC, ABAC, and ReBAC)
- Permit Elements (Embeddable UI components for user management and audit logs)
- OPAL-powered real-time policy and data syncing
- Policy-as-Code generation (Rego or Cedar)
Pros
- It uses a hybrid architecture, meaning decisions happen locally on your side with zero latency, but you still get a centralized cloud dashboard to manage it all.
- The embeddable UI components (Permit Elements) save you weeks of work since you don't have to build your own "Team Settings" or "Access Request" pages.
Cons
- The pricing is based on Monthly Active Users (MAUs), which can get a bit pricey if you have a massive user base but a tight budget.
- While the UI is great, if you’re a purist who wants to stay strictly in the code 100% of the time, the abstraction layer might feel like extra weight you don't need.
Ideal for: Product-led growth teams and developers who want to ship complex authorization features quickly without spending months building the backend and internal management tools.
Synk.to : Developer-First Identity & Security Visibility

I’ve had a good look at Synk, and it’s a smart choice if you’re tired of the "SaaS tax", those massive enterprise upgrades companies force on you just to get basic SCIM syncing.
It functions as a central brain for your identity stack, automating how users and groups move between different tools without you having to touch a line of code.
In terms of non-human identity management, it’s a big help for keeping your workspace clean, as it ensures that when a service account or bot is no longer needed, its access is actually cut off across every connected app in minutes.
Key Features
- Automated user and group provisioning: Handles the creation and management of accounts across your connected apps without manual work.
- SaaS identity sync: Keeps your user data consistent across tools like Slack and Jira without needing those expensive enterprise licenses.
- Identity lifecycle automation: Manages a digital identity from its initial creation all the way to its eventual deletion.
- Dormant account detection: Scans your stack to find accounts that aren't being used so you can kill the security risk and save on seat costs.
- Access review and auditing: Provides a single log of who can touch what, which makes compliance audits a lot less painful.
- Multi-SaaS governance: Gives you one dashboard to control security policies across your entire software ecosystem.
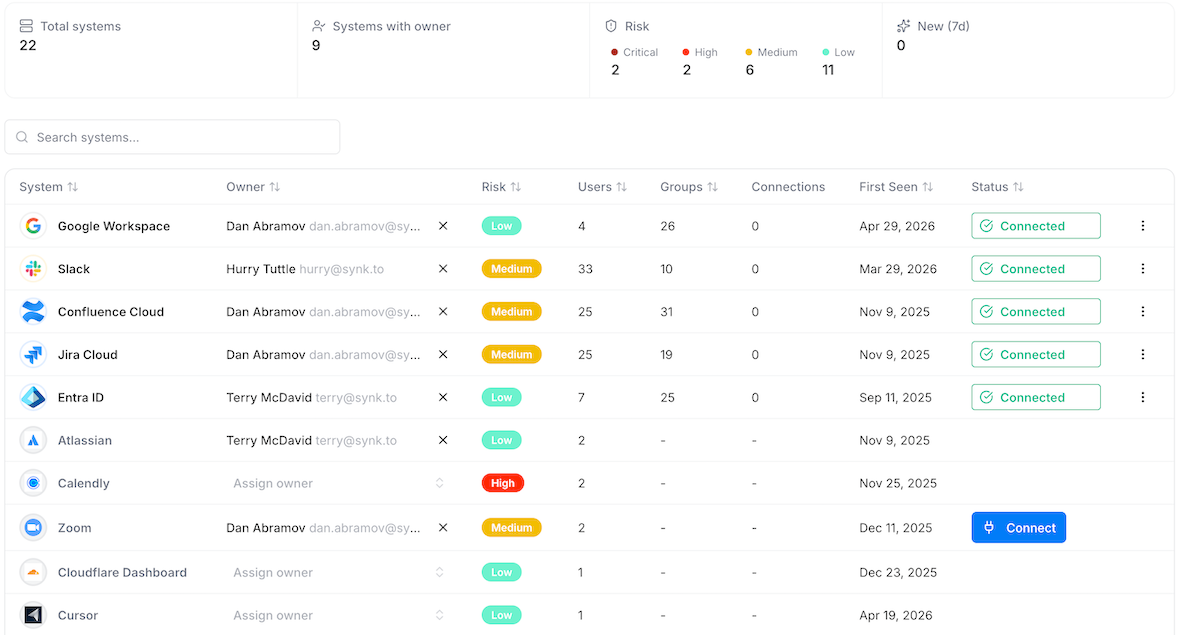
Pros
- It gives a helicopter view of all SaaS tools used in Google Workspace or Entre ID environments that are authorized and used by your employees without any approval (Shadow IT detection).
- It turns the headache of managing hundreds of SaaS systems and thousands of service accounts into a clean interface that feels as easy to use as a standard HR tool.
- The setup is built for speed (you can set it up in 5 minutes with only read-only access), allowing you to quickly identify risky systems and AI agent permissions without getting bogged down in weeks of custom coding.
Cons
- Since it sits in the middle of your apps, you have to monitor it as a critical part of your identity flow.
Ideal for: Growth-stage companies and IT teams that want to automate their identity governance without overpaying for enterprise SaaS plans.
Oso: Embedded Authorization Framework

Oso is a good pick if you’re tired of hardcoding permissions into every new feature. It basically pulls your authorization logic out of your core code and puts it into a declarative language called Polar.
This is a great help for managing machine credentials and those new AI agents everyone is deploying, since you can set up relationship-based rules.
Key Features
- Polar Declarative Policy Language
- Oso Cloud (Managed Authorization-as-a-Service)
- Native SDKs for Node.js, Python, Go, and Rust
- Model Context Protocol (MCP) Support for AI Tools
Pros
- You can change access rules in a Polar file without touching your app logic or redeploying the whole stack.
- The updates for AI agent security are great for preventing "rogue" bots.
Cons
- Your team has to learn Polar, which is easy enough but still another thing to manage.
- If you use the cloud version, you're putting a third-party service directly in your critical path for every request.
Ideal for: SaaS startups and teams that need to build complex, high-scale permissions for users and AI agents without the mess of manual coding.
WorkOS : Identity Infrastructure for SaaS
WorkOS quite a bit is basically a shortcut for any SaaS team that needs to look "enterprise-ready" without actually spending six months building it. It bundles SSO, directory syncing, and audit trails into a set of APIs that feel like they were actually written for developers.
Key Features
- Enterprise SSO (SAML & OIDC)
- Directory Sync (SCIM)
- AuthKit with AI-powered CLI installer
- Radar for bot and threat detection
- Admin Portal for customer self-service
Pros
- The Admin Portal lets your customers' IT admins set up their own connections, which saves your support team from constant back-and-forth emails.
- The free tier is actually useful, covering your first million monthly active users before you have to worry about a bill.
Cons
- You give up some control over the UI if you use the hosted AuthKit, though it’s customizable enough for most.
- You are relying on their infrastructure for your most critical login flows, so you better be okay with that dependency.
Ideal for: B2B SaaS startups that need to move upmarket and sell to big companies that demand SSO and automated provisioning.
Future Trends in Non-Human Identity Security
The security landscape is shifting fast as we move into 2026, making it clear that managing keys and service accounts isn't just a background task anymore. Here’s a quick look at where things are headed for those of us trying to stay ahead of the curve.
- AI-driven identity governance: Security teams are now using autonomous engines to monitor non-human identity management in real-time, catching weird behavior in service accounts before a human would even notice a spike.
- Rise of identity-first security models: Organizations are ditching the old "perimeter" mindset and putting the identity of the specific workload or bot at the very center of their entire defense strategy.
- Increased regulatory focus: New 2026 compliance standards are forcing companies to prove they have strict control and audit trails for every single machine credential and automated agent in their stack.
- Automation of identity lifecycle management: We’re seeing a big push toward "set-it-and-forget-it" workflows that handle everything from the birth of a token to its automatic rotation and eventual deletion without any manual intervention.
Final Thoughts
Modern infrastructure depends on service accounts and tokens to keep everything running, but leaving these identities unmanaged creates a huge opening for attackers.
Moving toward a proactive strategy for non-human identity management is the only way to stay ahead of these risks.
Using a platform like Synk.to will help you get that visibility directly into your existing dev workflow, so you can lock down your machine credentials and automated agents without breaking your deployment speed.
FAQ
What are non-human identities (NHIs)?
These are the credentials, like API keys and service accounts, that bots and automated scripts use to talk to other software. They handle the background work that keeps your apps and cloud services running without needing a human to log in.
Why are non-human identities a security risk?
They usually have way too much access and don't support multi-factor authentication, which makes them a goldmine for attackers. If a single token leaks, a hacker can often move through your entire system without anyone noticing.
How is NHIM different from traditional IAM?
IAM is built for people and passwords, but NHIM handles the millions of keys used by machines that scale way too fast for human management. You need a lot more automation here because machine identities change and multiply at a speed that would break a standard user directory.
What are the most common types of non-human identities?
You're mostly looking at OAuth tokens, API keys, and service accounts for cloud providers like AWS. It also covers the secrets hidden in your CI/CD pipelines and the private certificates that servers use to verify each other.
How can organizations secure non-human identities?
The smartest move is to rotate your keys constantly and make sure no bot has more access than it strictly needs to do its job. A platform like Synk.to helps by spotting these credentials in your code before they ever get deployed to the cloud.
What tools are used for non-human identity management?
Developers often use secrets vaults like Doppler or Infisical to store keys, alongside specialized security scanners. Synk is a go-to for many teams as it identifies and fixes leaked machine credentials right where the code is actually being written.
What is the future of non-human identity management?
We're heading toward a world where AI handles the entire lifecycle of a machine identity, from creation to automatic deletion. Security is becoming "identity-first," meaning every automated workload will have its own unique, verifiable entity that is monitored in real-time.